Started in 2021 with a simple idea
We thought security audits shouldn't feel like reading government documents. So we built courses that actually show you what happens when code meets real attack patterns.

We thought security audits shouldn't feel like reading government documents. So we built courses that actually show you what happens when code meets real attack patterns.
Four years of refining course material, testing what works in real learning scenarios, and watching people go from confused to capable.
Course completions
Full audit scenarios
Say material is practical
Course modules available
Back in 2021, Bjorn was tired of explaining the same security concepts over and over at consulting gigs. The documentation existed, but nobody actually read it. He figured there had to be a better way.
Started with five video walkthroughs of common audit mistakes. Put them online just to test the format. Within two months, 300 people had watched them and 80 asked for more.
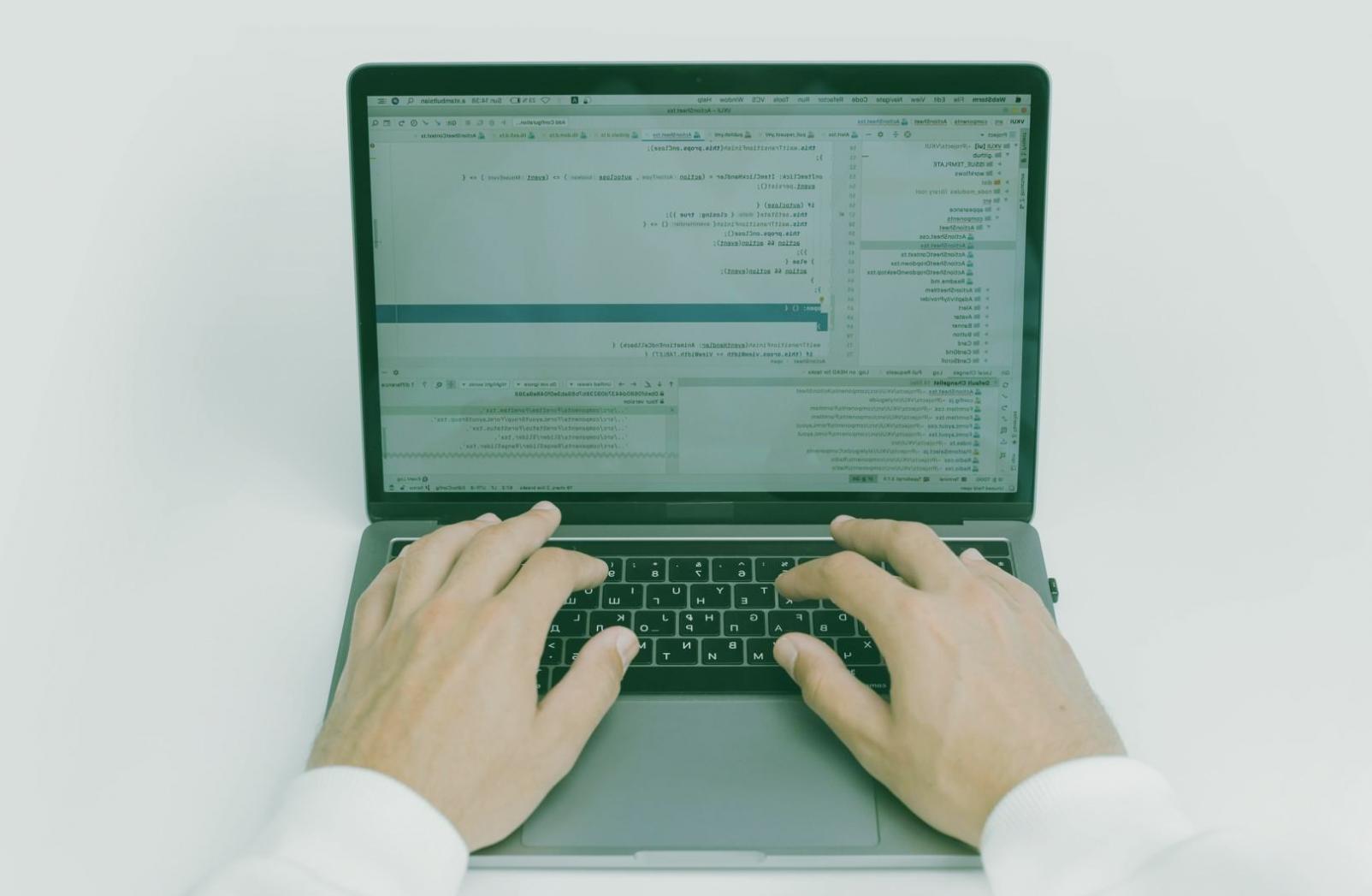
We don't teach theory first and application later. Every lesson starts with a real codebase that has actual vulnerabilities. You run the audit tools, see what breaks, understand why it matters.
No certification promises. No career transformation claims. Just the technical skills you need to spot security issues before they become production incidents.
We teach what we've personally debugged, patched, or spent late nights fixing in production environments.

Most web vulnerabilities happen because developers trust user input too much. Our courses walk through actual injection points, show you how fuzzing works in practice, and demonstrate what happens when sanitization fails.
You'll work with intentionally broken applications. Fix them. Break them again. Learn why certain patterns keep appearing in CVE databases.

REST APIs have different attack surfaces than traditional web apps. Rate limiting isn't just about preventing DDoS. Authorization checks need to happen on every endpoint, not just login.
We teach you to read API specs, spot missing authentication headers, test for mass assignment vulnerabilities, and find endpoints that leak more data than they should.
Password requirements mean nothing if reset tokens are predictable. Two-factor authentication fails when backup codes are stored in plaintext. We show you where authentication systems actually break.
Course material covers JWT vulnerabilities that still appear in 2024, session fixation attacks that work against modern frameworks, and OAuth flows that developers consistently misconfigure.
SQL injection still works in 2024 because ORMs don't protect against everything. NoSQL databases have their own injection patterns. Database permissions are usually too broad.
You'll learn to spot dangerous query patterns, test blind SQL injection methodically, audit database user privileges, and understand why prepared statements aren't a complete solution.